Virtual Trusted Platform Module (vTPM) VM Migration
Overview
While Virtualization Based Security (VBS) and Virtual Trusted Platform Module (vTPM) provide important security protections for the VM, V2V helpers and guestfs require proper read and write access to the VM’s disks. Temporarily disabling these features ensures that migration and disk operations can proceed reliably.
Prerequisites
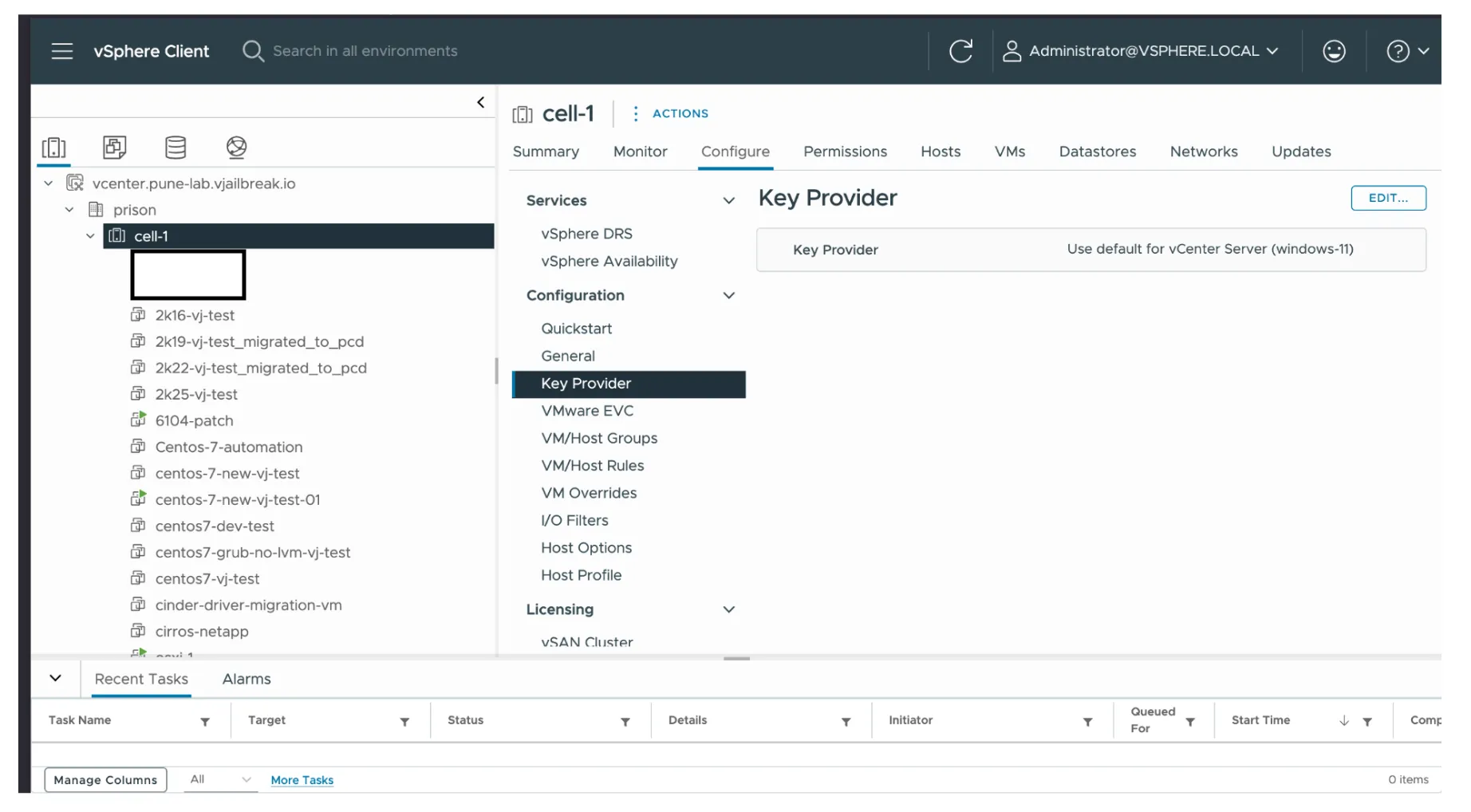
- VMware Native Key Provider (default vCenter-level key provider) must be configured for enabling vTPM on the source VM.
- On PCD, use
tpm_version: 2.0andtpm_provider: tpm-crbas extra metadata specs on the VM flavor to enable vTPM post migration.
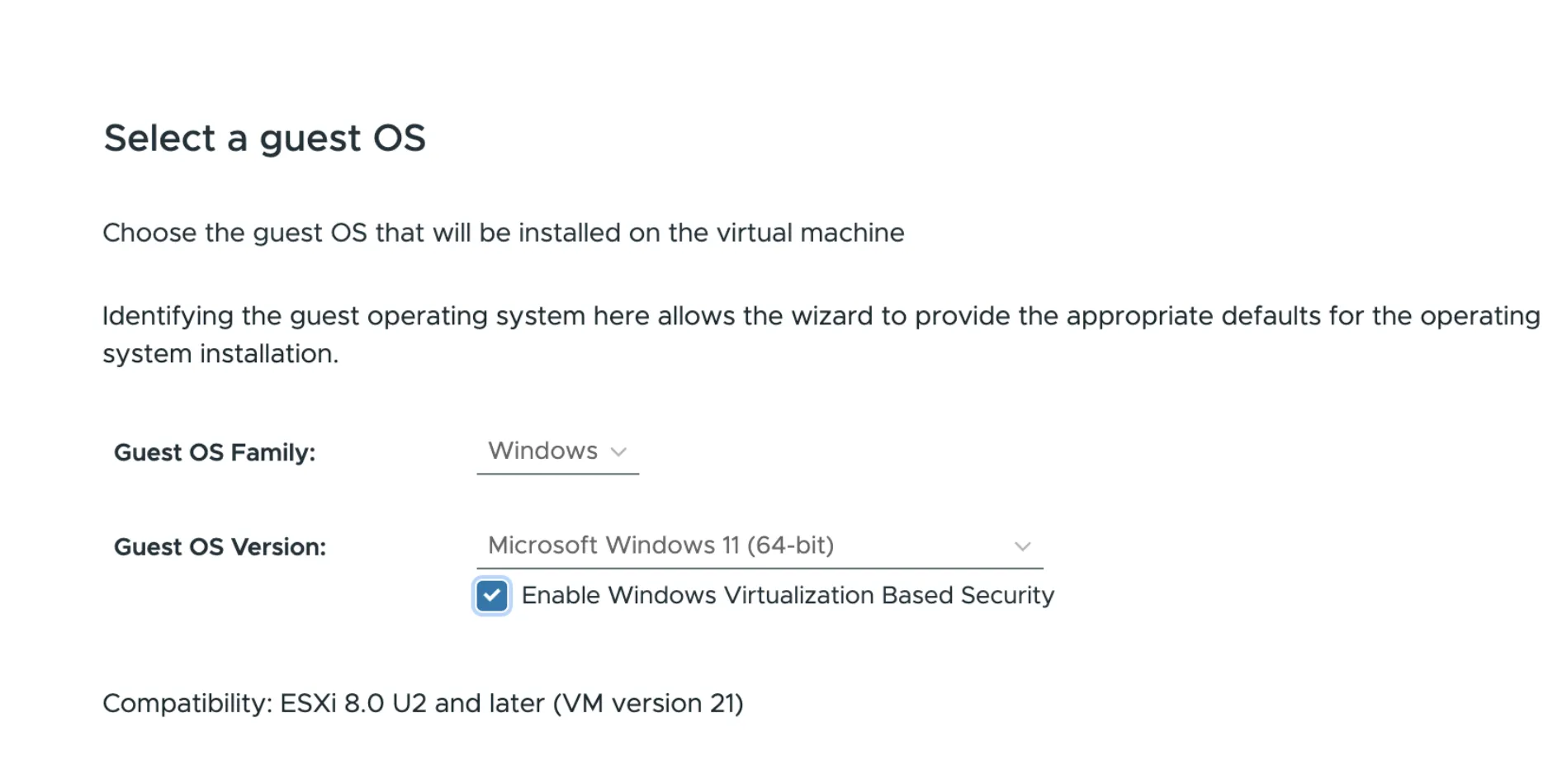
Enabling VBS and vTPM During Windows 11 Installation
When installing Windows 11, the user can enable VBS and vTPM at the OS selection stage by checking “Enable Windows Virtualization Based Security”.
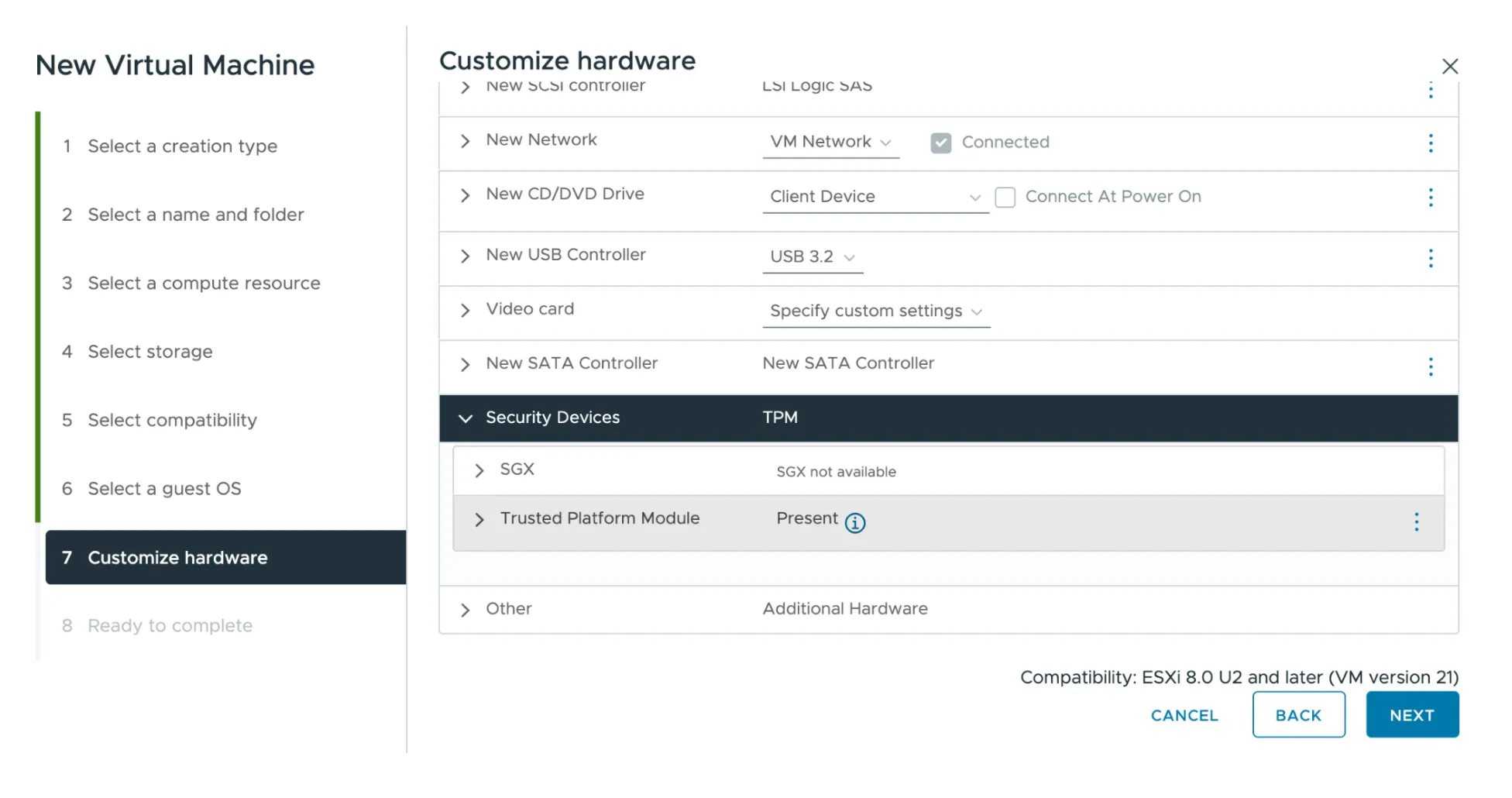
On the next stage (Customize hardware), you can verify that the Trusted Platform Module is present under Security Devices.
Pre-Migration Steps
Step 1: Power Off the Guest OS
Power off the guest OS on vCenter so that you can edit the VM settings and disable VBS and vTPM.
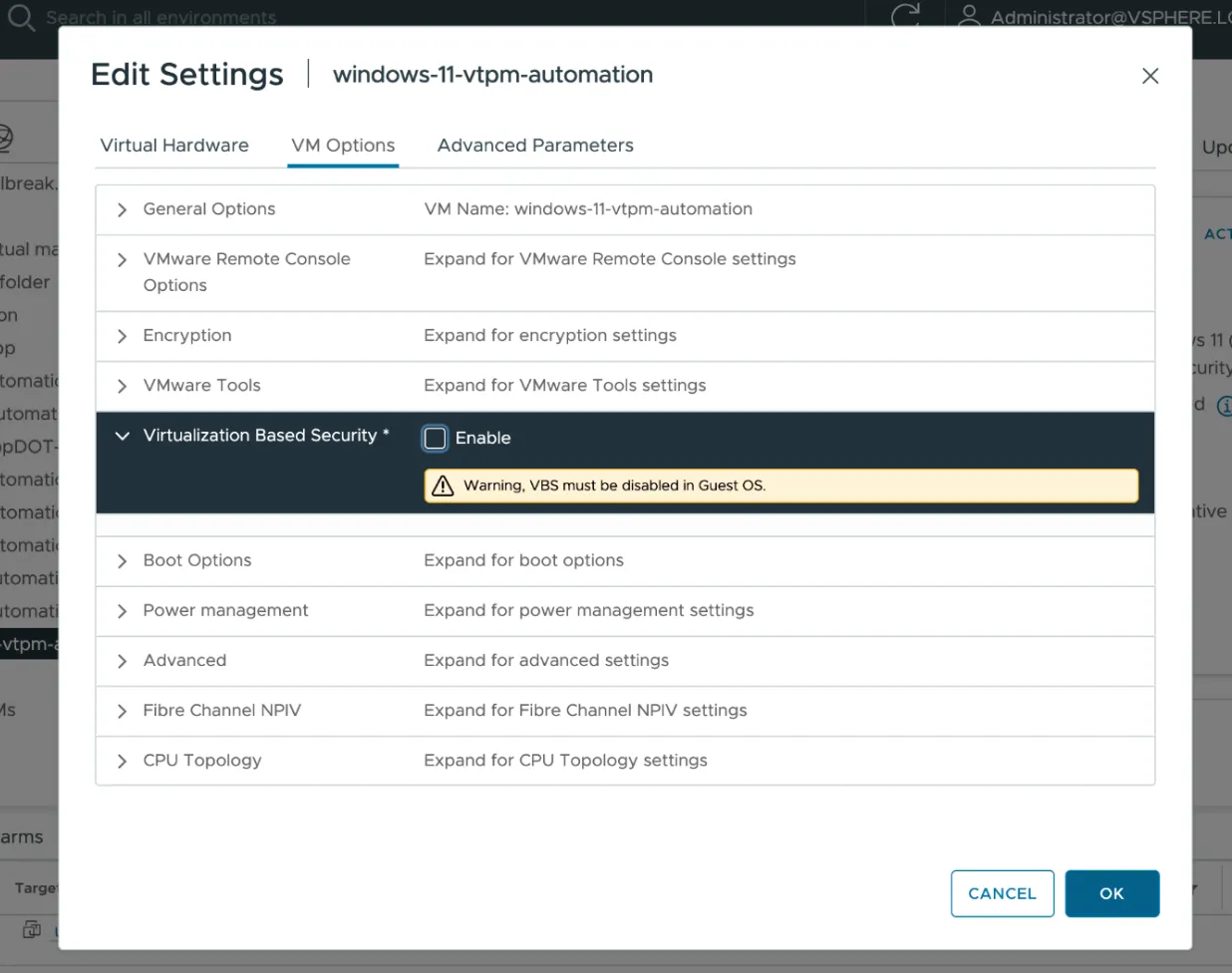
Step 2: Disable Virtualization Based Security
- Right-click the VM in vCenter and select Edit Settings.
- Navigate to the VM Options tab.
- Expand Virtualization Based Security and uncheck the Enable checkbox.
- Click OK to save.
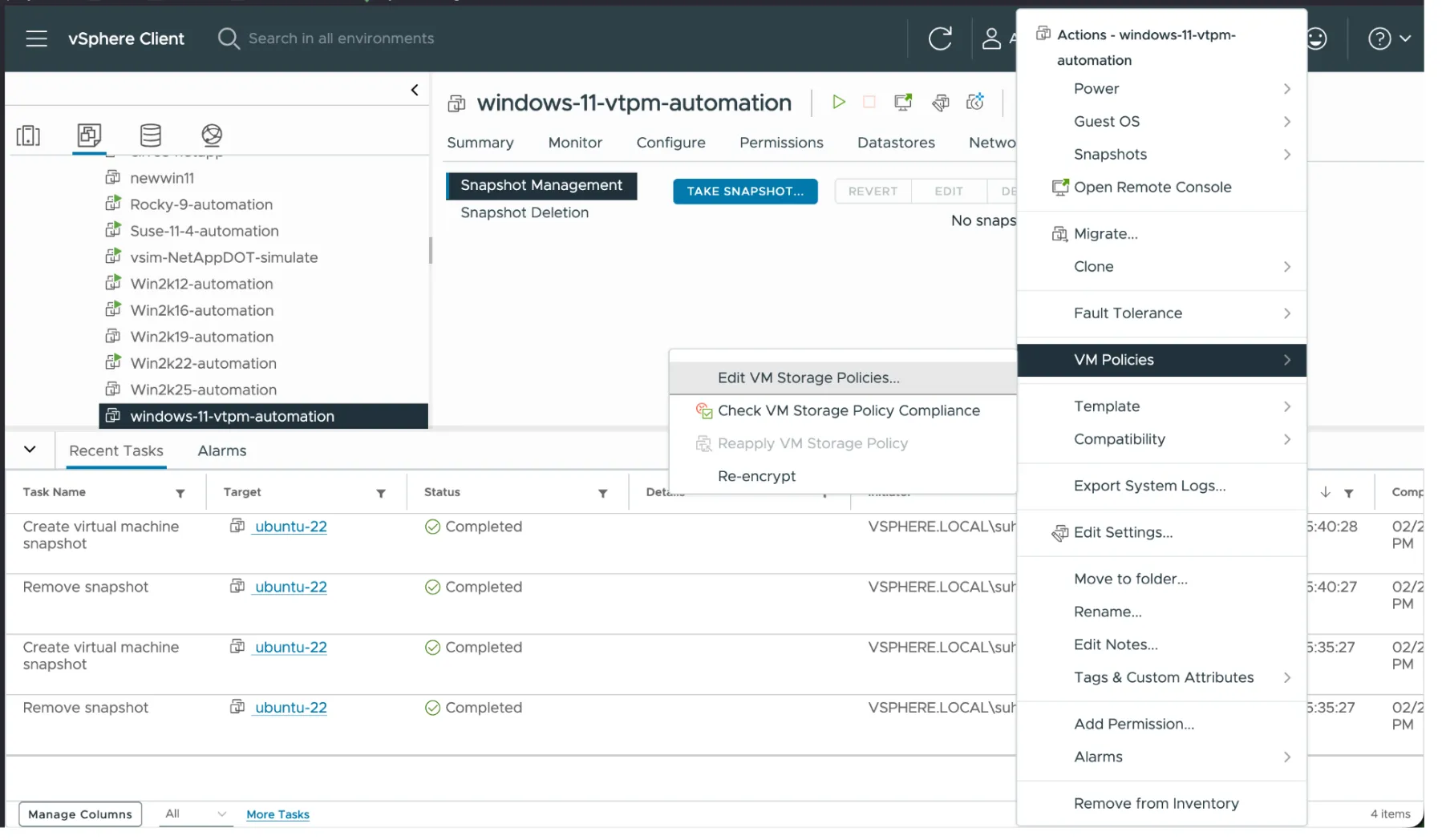
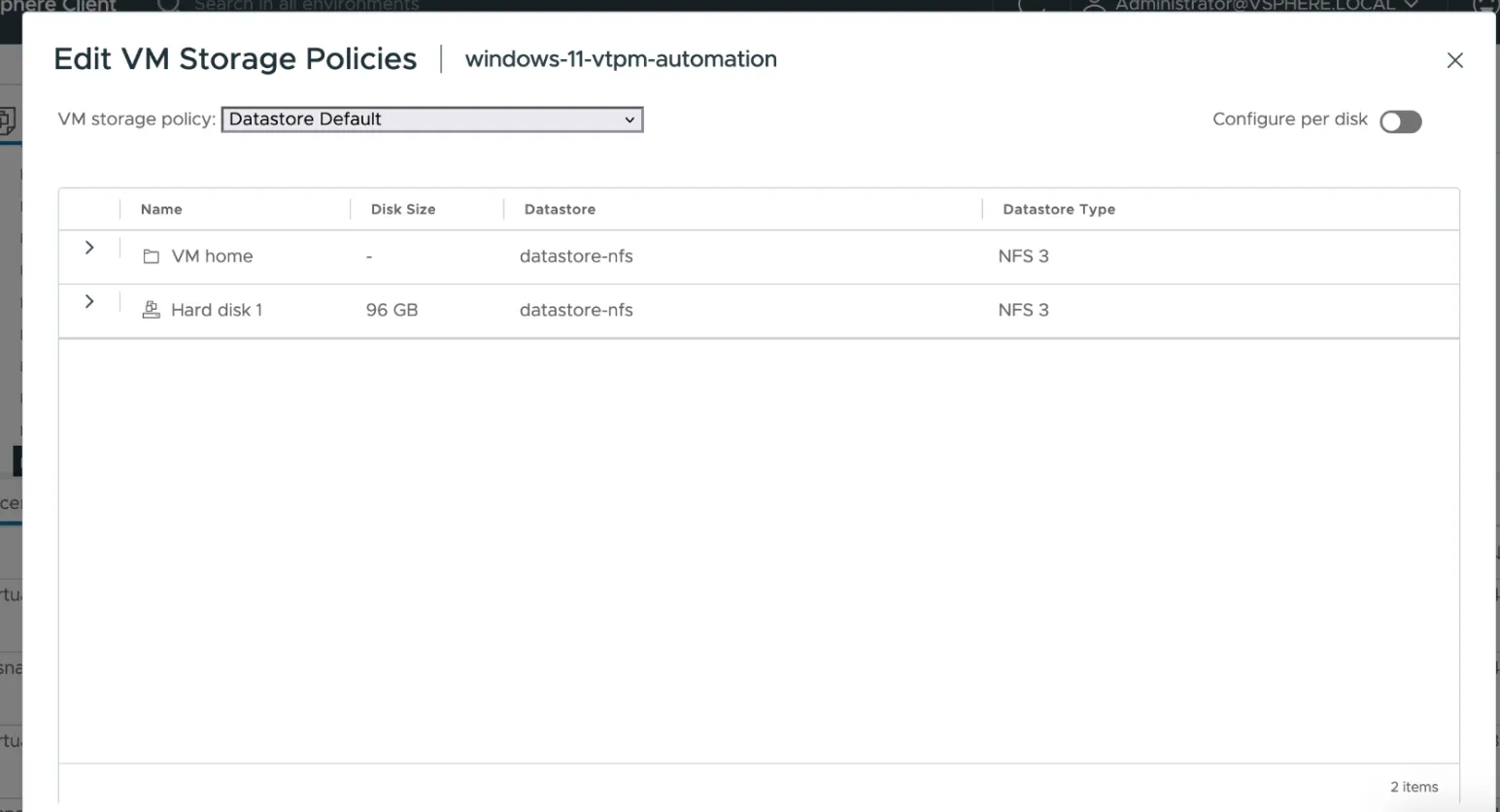
Step 3: Change VM Encryption Policies
Change the encryption policies of the VM to the Datastore Default policy:
- Right-click the VM in vCenter.
- Go to VM Policies → Edit VM Storage Policies.
- Set the VM storage policy to Datastore Default.
- Click OK to apply.
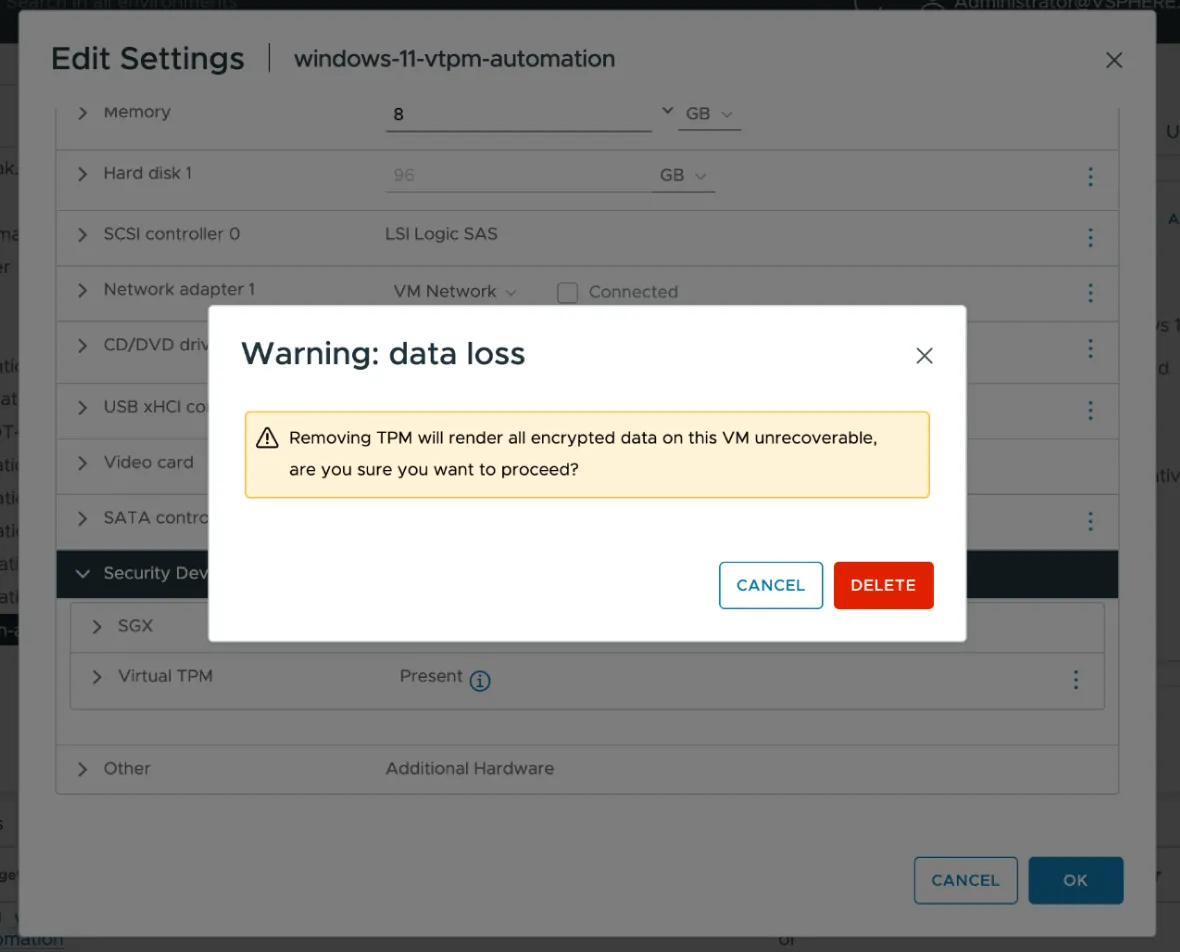
Step 4: Remove vTPM Device
- Right-click the VM in vCenter and select Edit Settings.
- Under Security Devices, locate the Virtual TPM device.
- Remove the vTPM device and confirm the deletion when prompted.
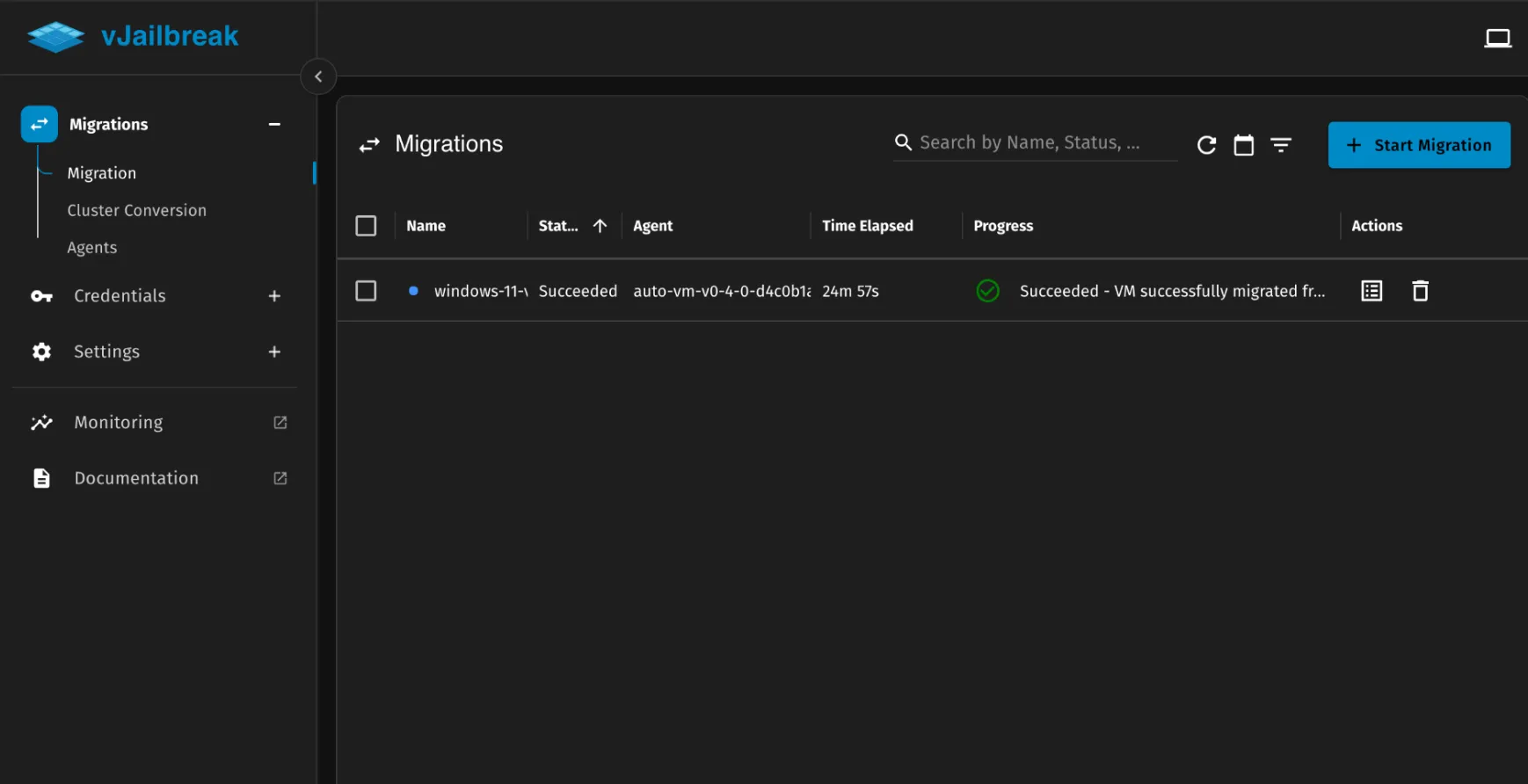
Start Migration
With VBS disabled, encryption policies reset, and the vTPM device removed, proceed with the migration using vJailbreak as usual.
Post-Migration Steps
After the migration completes successfully, re-enable vTPM on the VM in PCD by following the steps below.
Step 1: Reset PIN Using Backup Email
Since vTPM was removed before migration, the user will need to reset their PIN using the backup email configured earlier.
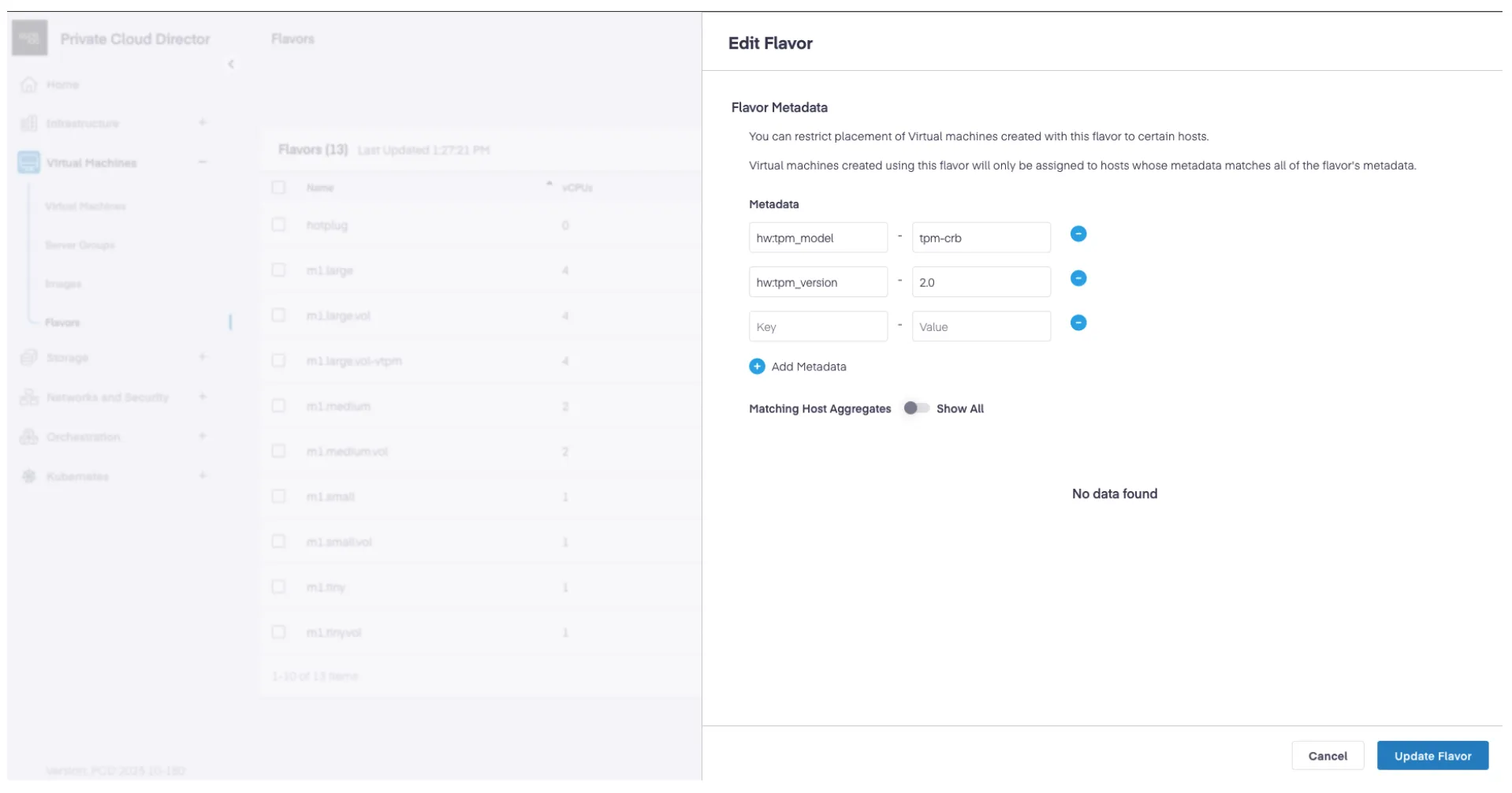
Step 2: Create a New Flavor with TPM Metadata
Create a new flavor (or update an existing one) with the same size as the migrated VM, adding the following TPM metadata:
| Key | Value |
|---|---|
hw:tpm_model | tpm-crb |
hw:tpm_version | 2.0 |
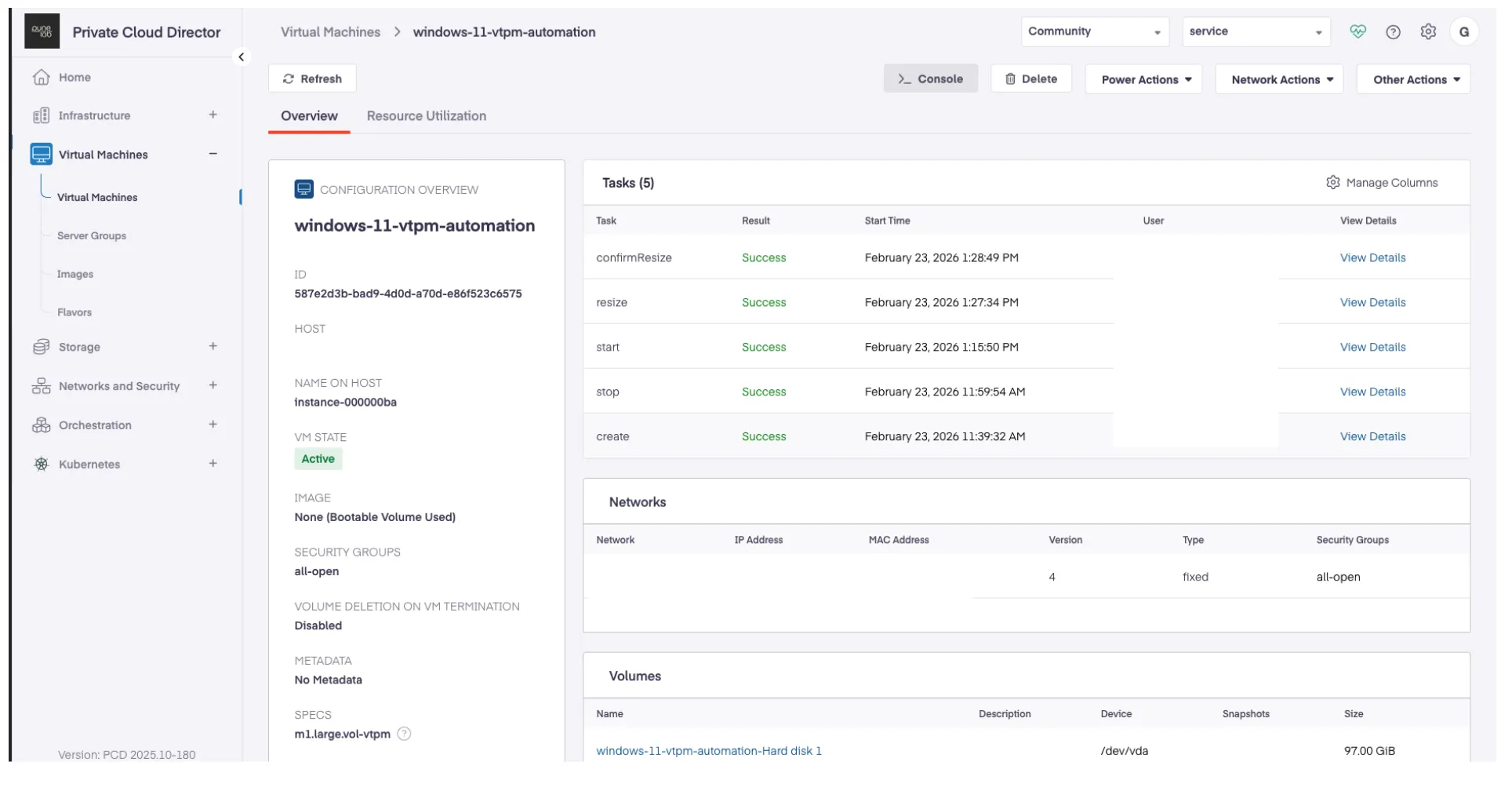
Step 3: Resize Migrated VM Using the TPM Flavor
- Navigate to the migrated VM in PCD.
- Resize the VM using the newly created flavor with TPM metadata.
- Confirm the resize operation.
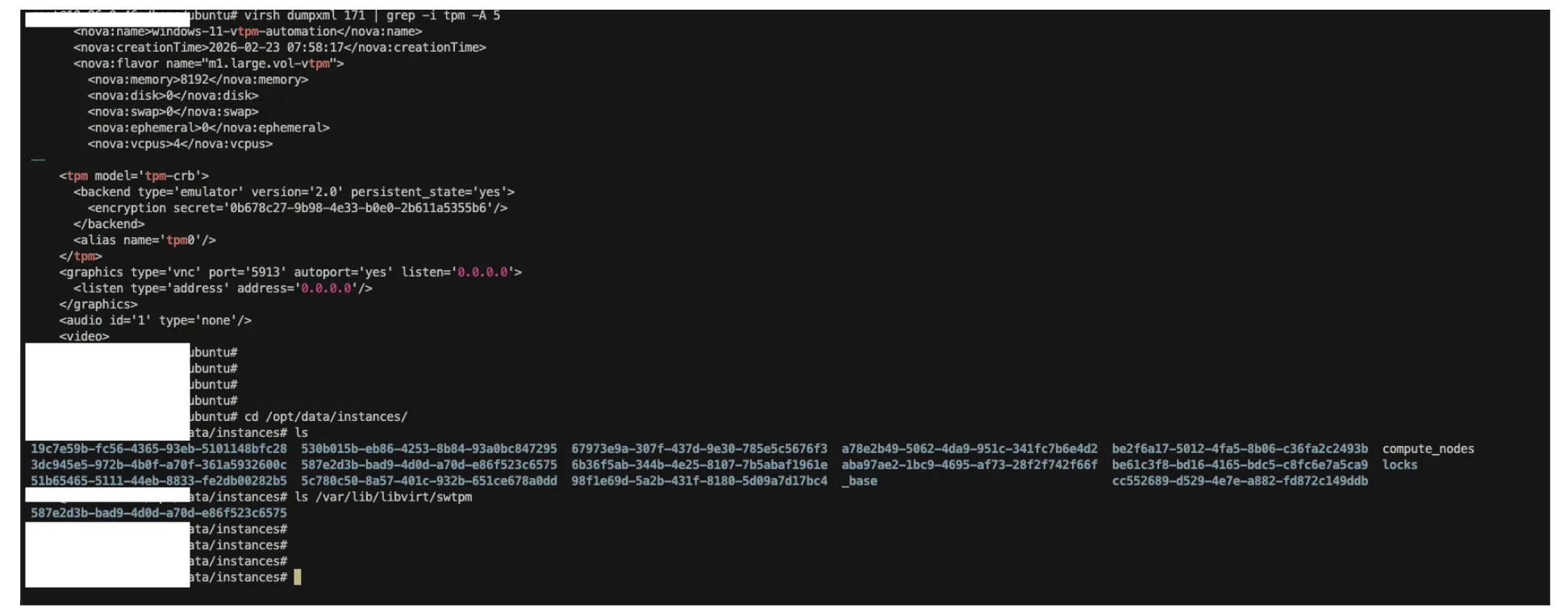
Step 4: Verify TPM is Enabled
After the resize completes, verify that TPM is enabled on the VM:
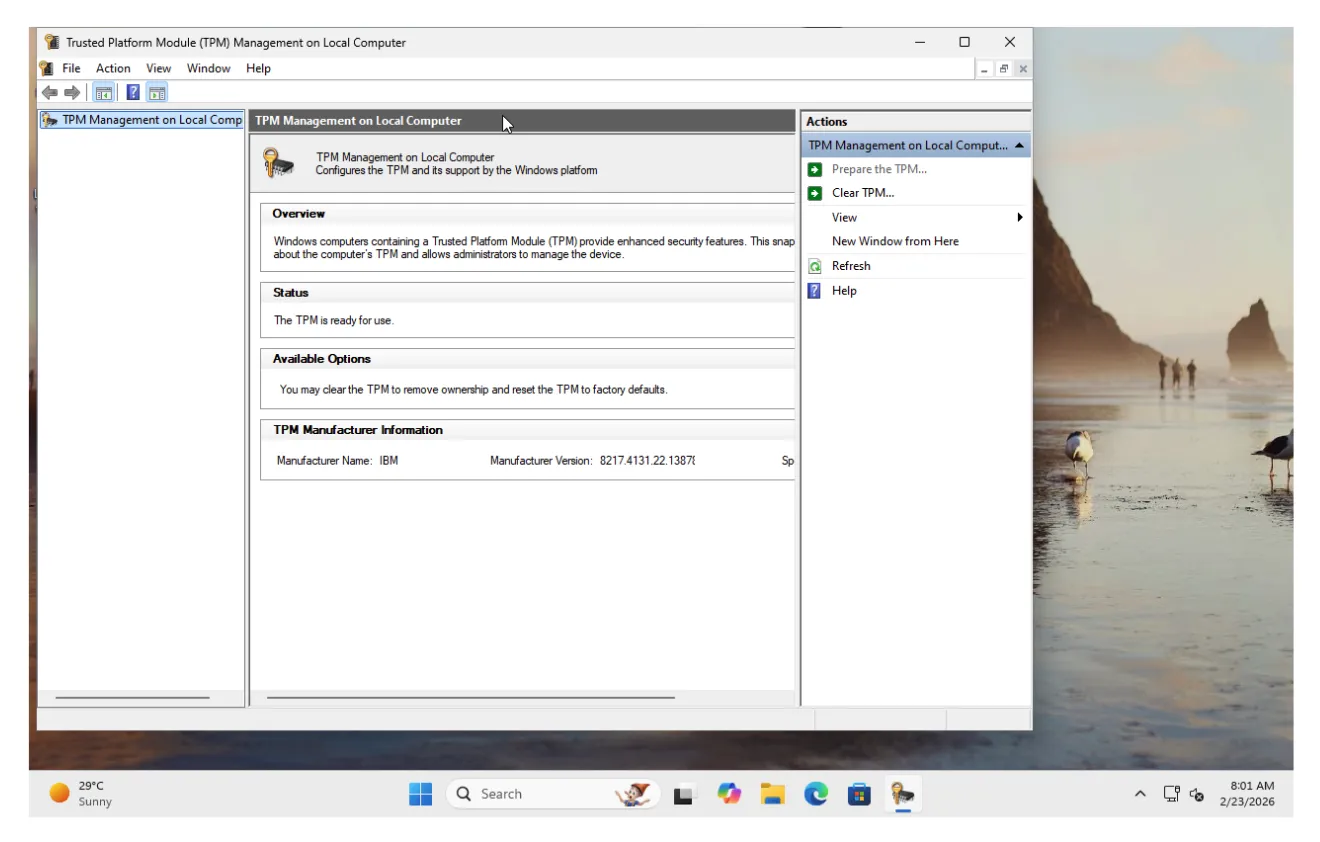
- From the hypervisor: Run
virsh dumpxml <instance> | grep -i tpmto confirm the<tpm model='tpm-crb'>block is present in the VM’s XML definition.
- From inside the VM: Open TPM Management (
tpm.msc) and verify that the TPM status shows “The TPM is ready for use.”